Building a Mature Vulnerability Management Programme

Vulnerability management starts simply enough. Run scans, fix what they find, repeat. Yet the journey from running scans to having a genuinely mature programme that drives meaningful risk reduction takes years, and most organisations stall somewhere along the way. Understanding what mature vulnerability management actually looks like, and the steps to get there, separates programmes that consume budget from programmes that earn their keep.
Maturity Has Levels
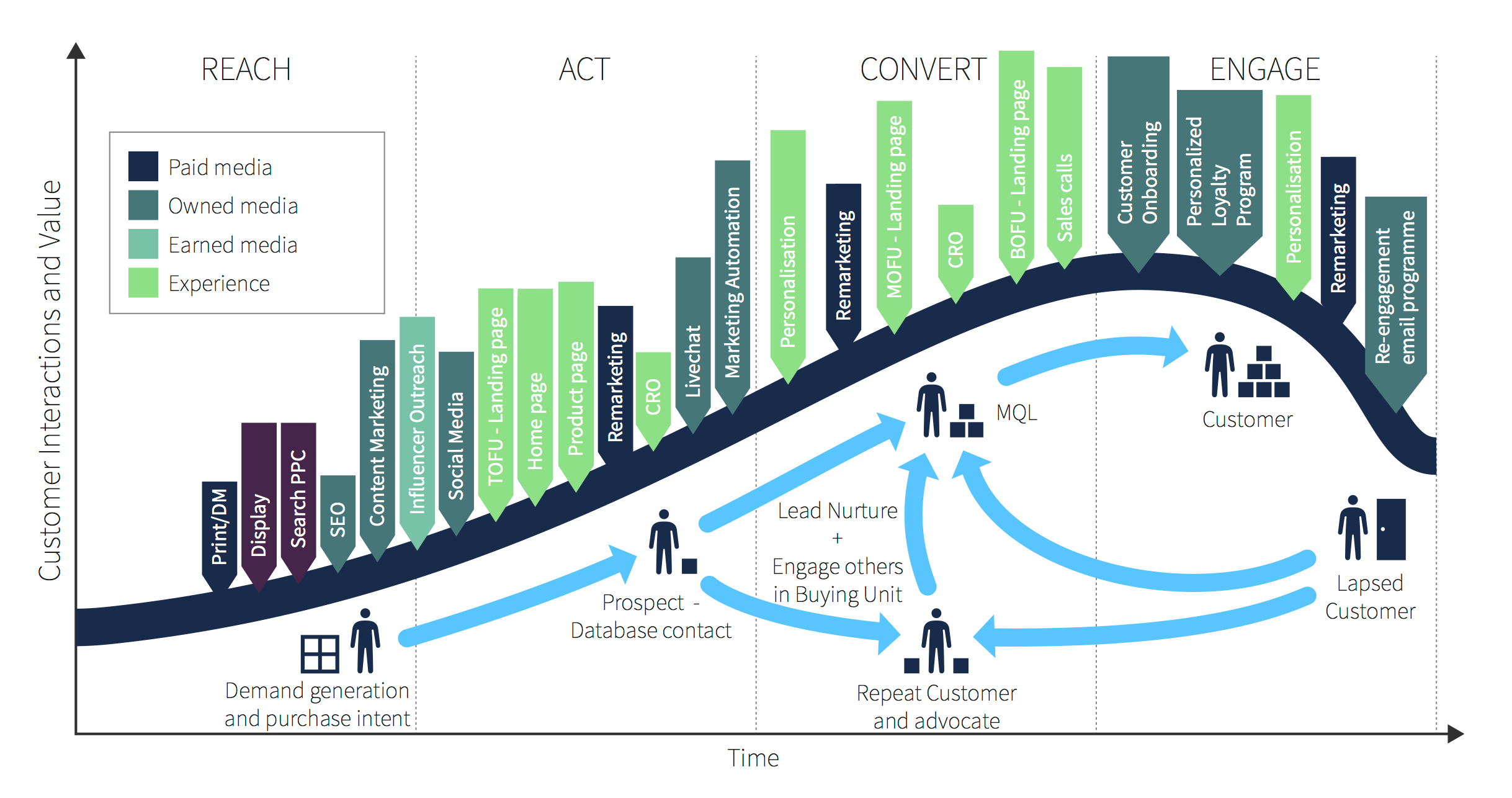
Early-stage programmes focus on coverage: scan everything, produce reports, hand them to whoever owns the affected systems. Mid-stage programmes add prioritisation, asset context, and remediation tracking, so that the work focuses on issues that matter most. Mature programmes integrate with patch management, threat intelligence, and business risk frameworks, producing a continuous flow of risk reduction rather than periodic spikes of remediation activity. Each level requires different investments and produces different outcomes.
Asset Inventory Is the Foundation
Without an accurate asset inventory, vulnerability management becomes scanning whatever happens to be reachable. Maturity depends on knowing what should exist, who owns each asset, what business function it supports, and what data it processes. Vulnerability scanning services programmes that incorporate asset discovery alongside vulnerability assessment build the inventory continuously rather than treating it as a separate exercise.
Prioritisation Beyond CVSS Scores
Raw CVSS scores rank vulnerabilities by theoretical severity but fail to account for context. A critical vulnerability on an isolated test system carries less business risk than a medium vulnerability on a public-facing customer database. Mature prioritisation weighs exploitability, asset value, exposure, and threat intelligence to produce ranking that reflects actual risk. The CISA Known Exploited Vulnerabilities list, the EPSS scoring system, and your own internal asset criticality data all feed into this calculation.
Expert Commentary
Name: William Fieldhouse
Title: Director of Aardwolf Security Ltd
“The vulnerability management programmes I see succeed share a common trait: they have stopped chasing every red item on the dashboard. Instead, they focus relentlessly on the issues that combine real exploitability, real exposure, and real impact. The remaining noise gets handled in routine cycles rather than treated as crisis.”
Service Levels That Actually Drive Behaviour
Defining clear service levels for remediation, by severity and asset class, gives both security and operations teams something concrete to work towards. Critical vulnerabilities on internet-facing systems within forty-eight hours, high severity within seven days, medium within thirty, low into the backlog. Track the metrics monthly, report them to the board, and treat misses as process issues to investigate rather than blame to apportion.
Integration Beats Isolation
Mature programmes connect vulnerability data with other security signals. Threat intelligence highlights which vulnerabilities are being exploited in the wild. Endpoint detection identifies which assets show signs of compromise. Patch management feeds back which fixes have actually been applied. Configuration management surfaces drift that affects exploitability.
Validation Through Active Testing
Vulnerability management benefits from periodic validation through penetration testing. Are the assumptions baked into your prioritisation correct? Does fixing the issues you have prioritised actually reduce risk in the way you expect? A best penetration testing company that runs alongside the vulnerability programme provides honest answers, and the resulting calibration improves the programme over time.
The Long View
Vulnerability management maturity unfolds over years rather than weeks. The early gains come from coverage and basic remediation. The middle gains come from prioritisation and process improvement. The later gains come from integration and continuous calibration against real-world threats. Each stage matters, and skipping ahead rarely works.